Cryptocurrency
What is Cryptocurrency?
It is a digital token (currency units) designed to work as a secure virtual currency created, exchanged, and regulated by its users (nodes) in a decentralized manner. It uses Peer to Peer (P2P) network for communication, cryptographic functions for security, and distributed ledger technology for transaction databases. Anyone is free to join or leave the cryptocurrency system at any time as there are no identities attached to users. Cryptocurrencies are digitally mined by each user for the creation of new digital tokens (virtual money) and also to verify the transaction. Each user can independently verify the entire transaction history as the ledger is shared among all users. This shared ledger consists of a chain of blocks composed of transactions that is regularly updated through the process of mining.
Working of Cryptocurrency
Cryptocurrency system works as follows
- Each user has a wallet with an address. This address is generated using a cryptographic function and acts as a public key.
- The wallet also contains a generated private key. It is used to sign transactions to prove ownership.
- The payer sends a digital token signed using the payer’s private key (virtual money) to the payee’s public key.
- The transaction is verified by mining.
Cryptocurrency Architecture has the following parts
- Network Protocol
- Consensus Protocol
- Transaction Protocol
- Internal State
Cryptographic Mining
Miners (users) are the most important part of the decentralized cryptocurrency network, and mining is an investment, just like trading. The miners are required to solve a resource-intensive task and this process is called mining. Mining is a brute-force algorithm and is designed to maintain the number of blocks mined per day remains approximately constant. Transactions are validated and appended to distributed public ledger through mining. A malicious miner may create multiple nodes and try to validate an invalid transaction. However, solving resource-intensive tasks makes it expensive for a malicious user to create sufficient false identities to outnumber benign miners and validate an invalid transaction.
The resource-intensive task performed by miners can be broadly classified into the following categories
- Proof of Work: that confirms the task has been performed.
- Proof of Stake: to show how much currency the miner owns in the system.
- Proof of Retrievability: to show that the given data to store is intact and can be recovered at will.
Steps involved in the mining are as follows
- Performs a resource-intensive task and produces proof that the work has been done. This prevents malicious miners from manipulating.
- The produced proof is verified to confirm that the task has been performed.
- The miner then checks for the validity of the transactions and the block is posted in the distributed ledger.
One-way functions are usually used for mining. The miner generates a nonce and tries hashing them with the hash of the previous blocks until the result follows a structure defined by the cryptocurrency.
Comparison of Traditional, Digital and Cryptocurrencies
In centralized banking, corporate boards or governments control the supply of currency by printing fiat currency. The traditional fiat currency payment system has some major drawbacks such as high transaction fees and longer settlement periods. This has led to alternative digital currencies. These currencies can be loyalty points or digital coins created by digital platforms. The creation, transaction, verification, and bookkeeping of the digital currencies are handled by institutions or legal entities. These alternative currencies provide shorter P2P processing time with lower settlement risk. However, these platform-based digital currencies are still centralized. Few are designed to support the business of the issuing institutions used as a substitute for fiat money because these are not legal tender. Other digital currencies are linked to centralized banking that can be bought or exchanged with legal fiat currency.
The decentralized cryptocurrency is a digital bearer asset in which the user (payer) who controls the respective private key owns a particular amount of cryptocurrency associated with the corresponding public key (payee). They are not bound to a particular location or jurisdiction; the integrated global payment network can be used to transfer irreversible funds all over the world. A community of mutually distrustful users referred to as miners use their computers to maintain the safety, integrity, and balance of ledgers. Compared with ordinary currencies held by financial institutions, cryptocurrencies are believed to be difficult for seizure and censorship by law enforcement due to underlying cryptographic technologies. In cryptocurrency, users are only identified by their public key. Therefore, privacy and security breaches are avoided as no personally identifiable information such as contact details, credit card numbers, and passwords are stored on servers. The legal status of cryptocurrencies varies as some countries have allowed their use and trade in exchange for actual currency, while others have banned or restricted it. Finally, some cryptocurrency systems can also be used for non-monetary use cases such as decentralized domain name registry, computing platform, and time stamping.
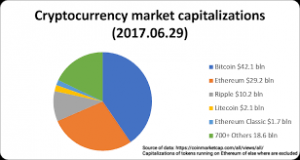
List of topmost cryptocurrencies
Although there are thousands of cryptocurrencies, only important ones are listed below
- Bitcoin: It was the first major usable cryptocurrency that started around the year 2009. It is the most familiar one with the highest market cap. Miners use the Hashcash mining method with the SHA-256 algorithm.
- Litecoin: Litecoin was the first cryptocurrency to use Scrypt for mining. It relies on the time-memory trade-off for mining. Proof of Work is achieved by memory-intensive operations compared to computationally intensive operations of Bitcoin.
- Ethereum: Ethereum was started in the year 2014 through crowdfunding. It did not use any pre-existing hash algorithm and developed its hashing algorithm named as EtHash to avoid mining centralization.
- Ripple: It does not use a Blockchain to reach a consensus for transactions. Instead, it uses an iterative trusted based consensus process, which makes it faster than Bitcoin. It uses the Elliptic Curve Digital Signature algorithm for mining.
- Peercoin: Mining uses Proof of Work and Proof of Stake. The Double-SHA-256 algorithm is used for Proof of Work.
- IOTA: It is a popular open-source cryptocurrency with many big companies embracing it. Tangle a breakthrough ledger technology is used and it requires the sender in a transaction to do a Proof of Work that approves two transactions. Thus, IOTA has removed dedicated miners from the process.